How do I get started with bug bounty hunting? How do I improve my skills?
These are some simple steps that every bug bounty hunter can use to get started and improve their skills:
Learn to make it; then break it!
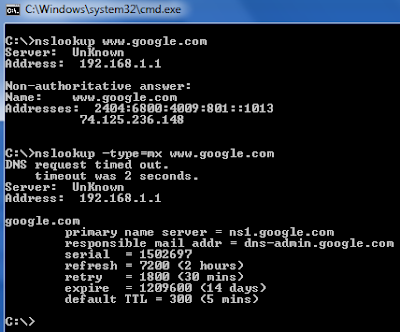
A major chunk of the hacker's mindset consists of wanting to learn more. In order to really exploit issues and discover further potential vulnerabilities, hackers are encouraged to learn to build what they are targeting. By doing this, there is a greater likelihood that hacker will understand the component being targeted and where most issues appear. For example, when people ask me how to take over a sub-domain, I make sure they understand the Domain Name System (DNS) first and let them set up their own website to play around attempting to "claim" that domain.
Read books. Lots of books.
One way to get better is by reading fellow hunters' and hackers' write-ups. Follow /r/netsec and Twitter for fantastic write-ups ranging from a variety of security-related topics that will not only motivate you but help you improve. For a list of good books to read, please refer to "What books should I read?".
Join discussions and ask questions.
As you may be aware, the information security community is full of interesting discussions ranging from breaches to surveillance, and further. The bug bounty community consists of hunters, security analysts, and platform staff helping one and another get better at what they do. There are two very popular bug bounty forums: Bug Bounty Forum and Bug Bounty World.
Participate in open source projects; learn to code.
Go to https://github.com/explore or https://gitlab.com/explore/projects and pick a project to contribute to. By doing so you will improve your general coding and communication skills. On top of that, read https://learnpythonthehardway.org/ and https://linuxjourney.com/.
Help others. If you can teach it, you have mastered it.
Once you discover something new and believe others would benefit from learning about your discovery, publish a write-up about it. Not only will you help others, you will learn to really master the topic because you can actually explain it properly.
Smile when you get feedback and use it to your advantage.
The bug bounty community is full of people wanting to help others so do not be surprised if someone gives you some constructive feedback about your work. Learn from your mistakes and in doing so use it to your advantage. I have a little physical notebook where I keep track of the little things that I learnt during the day and the feedback that people gave me.
Learn to approach a target.
The first step when approaching a target is always going to be reconnaissance — preliminary gathering of information about the target. If the target is a web application, start by browsing around like a normal user and get to know the website's purpose. Then you can start enumerating endpoints such as sub-domains, ports and web paths.
A woodsman was once asked, "What would you do if you had just five minutes to chop down a tree?" He answered, "I would spend the first two and a half minutes sharpening my axe."
As you progress, you will start to notice patterns and find yourself refining your hunting methodology. You will probably also start automating a lot of the repetitive tasks.
These are some simple steps that every bug bounty hunter can use to get started and improve their skills:
Learn to make it; then break it!
A major chunk of the hacker's mindset consists of wanting to learn more. In order to really exploit issues and discover further potential vulnerabilities, hackers are encouraged to learn to build what they are targeting. By doing this, there is a greater likelihood that hacker will understand the component being targeted and where most issues appear. For example, when people ask me how to take over a sub-domain, I make sure they understand the Domain Name System (DNS) first and let them set up their own website to play around attempting to "claim" that domain.
Read books. Lots of books.
One way to get better is by reading fellow hunters' and hackers' write-ups. Follow /r/netsec and Twitter for fantastic write-ups ranging from a variety of security-related topics that will not only motivate you but help you improve. For a list of good books to read, please refer to "What books should I read?".
Join discussions and ask questions.
As you may be aware, the information security community is full of interesting discussions ranging from breaches to surveillance, and further. The bug bounty community consists of hunters, security analysts, and platform staff helping one and another get better at what they do. There are two very popular bug bounty forums: Bug Bounty Forum and Bug Bounty World.
Participate in open source projects; learn to code.
Go to https://github.com/explore or https://gitlab.com/explore/projects and pick a project to contribute to. By doing so you will improve your general coding and communication skills. On top of that, read https://learnpythonthehardway.org/ and https://linuxjourney.com/.
Help others. If you can teach it, you have mastered it.
Once you discover something new and believe others would benefit from learning about your discovery, publish a write-up about it. Not only will you help others, you will learn to really master the topic because you can actually explain it properly.
Smile when you get feedback and use it to your advantage.
The bug bounty community is full of people wanting to help others so do not be surprised if someone gives you some constructive feedback about your work. Learn from your mistakes and in doing so use it to your advantage. I have a little physical notebook where I keep track of the little things that I learnt during the day and the feedback that people gave me.
Learn to approach a target.
The first step when approaching a target is always going to be reconnaissance — preliminary gathering of information about the target. If the target is a web application, start by browsing around like a normal user and get to know the website's purpose. Then you can start enumerating endpoints such as sub-domains, ports and web paths.
A woodsman was once asked, "What would you do if you had just five minutes to chop down a tree?" He answered, "I would spend the first two and a half minutes sharpening my axe."
As you progress, you will start to notice patterns and find yourself refining your hunting methodology. You will probably also start automating a lot of the repetitive tasks.
Related articles
- Blackhat Hacker Tools
- Blackhat Hacker Tools
- Hacking Apps
- Pentest Tools For Ubuntu
- Easy Hack Tools
- Blackhat Hacker Tools
- Pentest Tools Review
- Hacker Tools Linux
- Pentest Tools Online
- Hack Tools For Windows
- Hacking Tools Mac
- Tools For Hacker
- Pentest Tools Github
- Pentest Tools Github
- Pentest Tools Free
- Pentest Tools Kali Linux
- Hacking Tools For Pc
- Hack Tools Online
- Pentest Tools For Ubuntu
- Hacker Tools 2020
- Tools 4 Hack
- Hacking Tools Software
- Pentest Tools
- Pentest Tools Subdomain
- Pentest Tools List
- Nsa Hack Tools Download
- Hacking Tools Name
- Growth Hacker Tools
- Hacker Search Tools
- How To Hack
- Hacking Apps
- Usb Pentest Tools
- Hacker Tools For Ios
- Hack Tool Apk
- Easy Hack Tools
- Pentest Tools For Windows
- Pentest Tools Free
- Ethical Hacker Tools
- Hack Tools Pc
- Hack Tools 2019
- Pentest Tools Nmap
- Hacker Security Tools
- Pentest Tools List
- Pentest Tools Windows
- What Are Hacking Tools
- Hack Tools Download
- Pentest Tools Url Fuzzer
- Hacker Tools Software
- Hacker Security Tools
- Hacker Tools
- Hacker Tools Mac
- Hacker Tools Free
- Pentest Tools Android
- Hacking Tools For Beginners
- Hacking Tools Kit
- Hack Tool Apk No Root
- Hack App
- Hak5 Tools
- Hack Tools Online
- Top Pentest Tools
- Hak5 Tools
- Pentest Tools Review
- Black Hat Hacker Tools
- Hacking Tools Software
- Computer Hacker
- Pentest Tools Website Vulnerability
- Pentest Tools For Windows
- Pentest Tools For Mac
- Hacker Tools Online
- Kik Hack Tools
- Hacker Tools Online
- How To Make Hacking Tools
- Hacker Tools Free
- Pentest Tools For Ubuntu
- How To Hack
- Best Hacking Tools 2019
- Underground Hacker Sites
- Hacking Tools Pc
- Hack Tools For Pc
- Tools 4 Hack
- Hacking Tools Name
- Hacker Tools Free Download
- Hack Tools For Windows
- Tools 4 Hack
- Hacking Tools 2019
- Best Hacking Tools 2020
- Hack Tools Download
- Hacking Tools Hardware
- Hacker Tools 2019
- Hacker Tools Windows
- Computer Hacker
- Hack And Tools
- Hacker
- Pentest Tools Framework
- Pentest Tools Website
- Pentest Box Tools Download
- Pentest Tools List
- Hack Apps
- Pentest Tools Framework
- Pentest Tools For Ubuntu
- Hacking Tools 2019
- Install Pentest Tools Ubuntu
- Hack Tools 2019
- How To Make Hacking Tools
- Hacking Tools Free Download
- Best Hacking Tools 2020
- Pentest Recon Tools
- Hacking Tools For Games
- Pentest Tools Free
- Hack Tool Apk
- What Is Hacking Tools
- Pentest Tools Port Scanner
- Hacker Techniques Tools And Incident Handling
- Termux Hacking Tools 2019
- Pentest Tools List
- Pentest Tools Find Subdomains
- Pentest Tools Github
- Bluetooth Hacking Tools Kali
- Hacker Tools
- Nsa Hacker Tools
- Tools 4 Hack
- Hacker Tools List
- Hacking Tools Windows 10
- How To Install Pentest Tools In Ubuntu
- Hacking App
- Hack Tools For Ubuntu
- Top Pentest Tools
- Blackhat Hacker Tools
- Hack Tools For Mac
- Hacking Tools Hardware
- Underground Hacker Sites
- Hack Tools 2019
- Hacker Tools For Ios
- Hack Tools
- Hacking App
- Hack Tools 2019
- Hacking Tools For Mac
- Hacker Tools 2020
- Pentest Tools Open Source
- New Hack Tools
- Pentest Tools Apk
- Hacker Tools Hardware
- Growth Hacker Tools
- Hack Tool Apk